Employers that sponsor group health plans (medical, dental, vision, HFSA) are used to negotiating detailed administrative services agreements with vendors that provide services to those plans. Many also are familiar with “business associate agreements” required under HIPAA that must be in place with certain vendors, such as third-party claims administrators (TPAs), wellness program vendors, benefits brokers, etc. However, many plan sponsors may not be aware of a contract requirement with respect to the confidentiality of patient records relating to a substance use disorder (SUD). If applicable, these contract provisions must be in place by February 2, 2020.
Federal regulations (42 C.F.R. Part 2) provide specific protections for SUD patient records. In general, these are records held by certain SUD treatment programs, those that receive federal funding. The arm of the Department of Health and Human Services that regulates SUD programs, Substance Abuse and Mental Health Services Administration (“SAMHSA”), issued final regulations in 2018 concerning the confidentiality of SUD patient records. In a number of respects, these rules strengthen protections already in place under the HIPAA privacy and security rules.
How do the new SUD regulations affect contracts with health plan vendors?
Under Section 2.33 of the regulations, when a patient consents to a disclosure of their SUD patient records for payment and/or health care operations activities, the records may wind up with a “lawful holder” of those records (a plan sponsor, for example), and then on to the lawful holder’s third-party vendors to carry out the payment and/or health care operations on behalf of such lawful holder. When this happens, lawful holders must have in place a written contract with the third party obligating the third party to be bound by 42 C.F.R. Part 2.
The contract should require the third-party recipients of these records to implement appropriate safeguards to prevent unauthorized uses and disclosures, and to report any unauthorized uses, disclosures, or breaches. The contract also should prohibit the third party from re-disclosing the records unless the disclosure is to a contracted agent of the third party that is helping the third party provide services described in the contract, and any further disclosures are back to the third party or the lawful holder (plan sponsor).
In addition to the contract requirement, lawful holders must provide to such third parties a statement in connection with the disclosure, which may be as simple as “42 CFR Part 2 prohibits unauthorized disclosure of these records.”
What to do next?
Plan sponsors receiving SUD patient records in connection with their group health plan and sharing that information with a third-party service provider, or where the service provider is receiving such information on behalf of the plan sponsor, should review the provisions of their services agreements and, if applicable, business associate agreements. For plan sponsors not currently receiving SUD patient records, it may make sense to update these third-party contracts in the event such records are received. While updating these agreements, it may also be a good time to revisit other provisions to ensure strong contractual protections such as adding specificity on response to data incident, indemnification, limitation of liability, and other contractual protections.
 2020 may very well be the most impactful year for data privacy and cybersecurity in the United States. In honor of Data Privacy Day, we discuss some of the reasons why that may be the case. In short, as privacy and cybersecurity risks continue to emerge for organizations large and small, the law is beginning to catch up which is prompting a significant uptick in compliance efforts.
2020 may very well be the most impactful year for data privacy and cybersecurity in the United States. In honor of Data Privacy Day, we discuss some of the reasons why that may be the case. In short, as privacy and cybersecurity risks continue to emerge for organizations large and small, the law is beginning to catch up which is prompting a significant uptick in compliance efforts.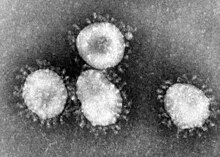 The outbreak of a new coronavirus that is believed to have began in central Chinese city of Wuhan and now appears to be spreading to the United States is driving concerns for organizations around preparedness regarding their operations, their customers, and their employees. Both the
The outbreak of a new coronavirus that is believed to have began in central Chinese city of Wuhan and now appears to be spreading to the United States is driving concerns for organizations around preparedness regarding their operations, their customers, and their employees. Both the  Businesses subject to the California Consumer Privacy Act (“CCPA”) are working diligently to comply with the law’s
Businesses subject to the California Consumer Privacy Act (“CCPA”) are working diligently to comply with the law’s